How To Hack Google? What we have learnt from (legally) hacking Google, Slack and Facebook
There is a saying that goes: There are two types of companies; those that have been hacked, and those that think they haven’t been hacked. Whether you like it or not, the Internet is broken from a security point of view, which is why it is crucial for you to figure out how vulnerable your business is, and find the best way to protect your customers.
Some companies have already realized the business value of security, making it a habit internally, and making it a central part of the customer experience. Other companies are stuck with common misconceptions about web security, such as I’m safe because nobody would want to hack us or We’re safe because our web agency handles our web development.
Reality check – over 92% of the companies we have performed security tests on are vulnerable. And if companies like Facebook, Paypal, Google etc. are vulnerable – why wouldn’t you be? There is a lot to learn from the hacks we have legally performed on many of the tech giants, and their reactions to our submitted vulnerability reports.
Google – utilize the white hat-hacker community
What we did: A couple of years ago, two of the startup founders, Fredrik A. and Mathias K., managed to get read access on Google’s production servers by uploading a malicious XML to one of the company’s servers. It later turned out to be a major XXE flaw (for any non-technical readers, you just understand that this is very bad). Google paid our team members a reward of $10.000 as a thank you, covering our team members’ road trip through Europe the same summer.
What you need to learn: Google was early to realize that doing everything yourself is impossible. They set up a Responsible Disclosure program that allowed ethical hackers to search for vulnerabilities on their own behalf, report them, and get some money for each reported security vulnerability. Many freelance security researchers were attracted by the concept and over the years it has resulted in a large number of resolved security issues.
If you choose to implement this yourself, there is no need to initially offer any monetary compensation for each submitted report. Step one would be to publish a way security researchers can contact you (e.g. a security email like [email protected]) and show appreciation when someone reports a vulnerability. To increase the incentive to help, consider publishing a list with the names of everyone that has contributed, a so-called “Security Hall of Fame”.
Slack – run a bug bounty and fix critical issues immediately, even on a Friday
What we did: Frans R., one of startup security researchers, was able to create a malicious page that could reconnect users’ Slack WebSocket to his own WebSocket in order to steal their private Slack tokens. The vulnerability would have allowed black-hat hackers to take over Slack accounts and read archives. Slack fixed the bug in 5 hours on a Friday and paid Frans $3,000 as a reward. Impressive!
What you need to learn: The timeline of the submitted vulnerability was a perfect example of security work and PR done right. A critical vulnerability doesn’t inevitably lead to a PR catastrophe. By quickly acting on the report, Slack’s team was able to turn the incident into something positive and their security work was praised in the media. Their quick reaction, even though the weekend was approaching, was exemplary and aligned with how the black hat-community works – security doesn’t stand still during weekends…
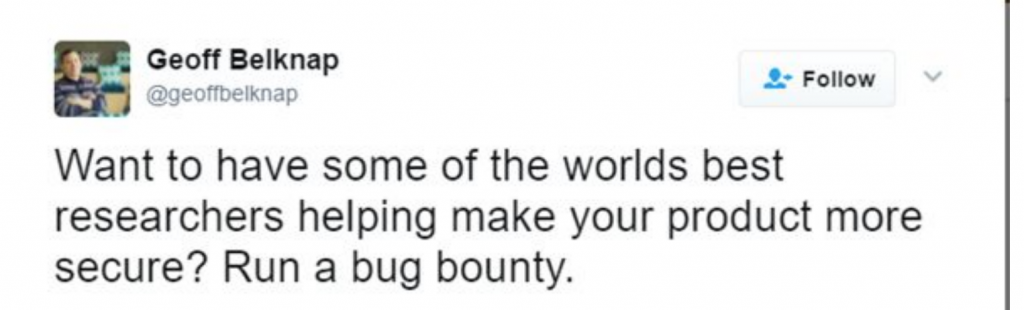
The other takeaway, which Slack’s CISO Geoff Belknap clearly stated on Twitter, is to run a bug bounty, and use the skills of the world’s best researchers to secure your product.
Facebook – be conscious of third-party vendors and connected services
What we did: Frans strikes again! This time, he found a stored XSS on Facebook, initially through a Dropbox sync, and later by expanding with other services like Pinterest. By using the files in his Dropbox, he managed to inject script code that was executed on Facebook.com. The vulnerability was later, of course, resolved promptly, and a bounty of $3,500 was paid to Frans.
What you need to learn: Frans was initially working on findings flaws on Dropbox when he stumbled across the vulnerability that was linked to Facebook. This is usually how hackers work. They go through third party extensions and plugins that are being used and services that are connected to your site. Your core website might secure, but companies seldom perform security checks on third-party vendors, integrations and linked service.
Who stands behind all this, you may ask?
A Swedish IT security startup, founded in 2013 by a group of top-ranked white-hat hackers. The company is a part of the ethical hacking community, and today, they utilize the knowledge of 100+ handpicked hackers from around the globe to keep their users safe.
Click here to read more community news.